
Solutions
Providing a flexible and scalable compute, storage and application platform. Automating services to improve operational and management efficiencies. Securely delivering IT resources on demand. Enabling fast and effective responsiveness to changing requirements.
Cloud Storage Infrastructure: Providing long term backup retention, limitless file archive, compliance repository, and disaster recovery data set.
Virtual Infrastructure: Replacing your physical infrastructures with virtual infrastructures – hardware becomes software.
Dynamic Applications: Improving scalability by utilizing dynamic application architecture. Allowing deployment of higher computing capacity when it is needed, and ability to scale back when it is not.
Flexible Data Processing Center: Deploying virtual capacities internally to meet the ebb and flow of workloads that need to be processed immediately
Host Based Security Solutions: Insuring intrusion detection and policy enforcement.
Virtual Infrastructure Security Solutions: Providing application level compliance, policy enforcement, and boundary control.
Advance Malware Detection & Remediation: Mitigating modern attacks with network sandboxing, dynamic code analytics, and zero day detect and protect.
Security Event Monitoring: Monitoring, correlation and analytics, proactive remediation and alerting.
Firewall & Perimeter Defenses: Tightly integrating both physical and virtual firewalls within the stack.
Cloud Access Security Broker: Monitoring, managing and enforcing rules upon the cloud services accessed by users.
Virtualization: Improving flexibility and dependability. Lowering capital expenditures. Running multiple operating systems. Securing desktop environments. Streamlining application deployments. Decoupling applications from underlying infrastructure.
Converge & Consolidate: Converged Infrastructure (CI), Hyper-Converged Infrastructure (HCI), Open Converged Infrastructure (OCI) – insuring compatibility between all components while reducing the costs for cabling, cooling, power and floor space. Software Defined Infrastructure (SDI) – automatically and efficiently servicing local, cloud, or hybrid cloud environments’ application workloads.
Data Reduction: Reducing hardware investment while improving performance and lowering power and cooling costs.
Doing all of the above with far less hardware.
Configuration Management: Reducing operational costs and infrastructure. Using automation tools to manage growth without increasing headcount.
Enterprise Management: Maximizing infrastructure stability. Gaining centralized control over storage, servers, and networks. Increasing efficiency and visibility. Eliminating the cost of managing multiple point tools.
Availability: Minimizing application downtime. Facilitating automated failover. Limiting reactive recovery.
Data Archiving: Improving application performance and manageability. Automating movement from higher-tiered storage to lower cost storage (SATA, tape, etc.).
Primary Storage (SAN/NAS): Improving availability, functionality, and performance of data infrastructure. Deploying a scalable array-based infrastructure. Making it easier to store, protect, and expand data.
WAN Optimization: Improving application performance over the WAN. Simultaneously decreasing bandwidth utilization. Enabling IT consolidation, optimizing disaster recovery, and centralizing management.
Flash Optimization: All Flash or Flash Optimized Hybrid – improving performance, simplifying operations, lowing environmental costs.
The technologies we use to make our organizations more productive, more secure, simpler to manage, quicker to deploy, and easier to scale – the evolution continues. Infrastructure continues to converge – services running at the application level, software defined everything (SDE), new threats, and new defenses.
As new vendors and new technologies come out of stealth and look to approach the federal government IT community they come to StorageHawk for help. We know the unique challenges of federal IT. We know the various missions, programs and initiatives and where emerging technologies have the biggest impact with the least risk.
Full Life Cycle Support
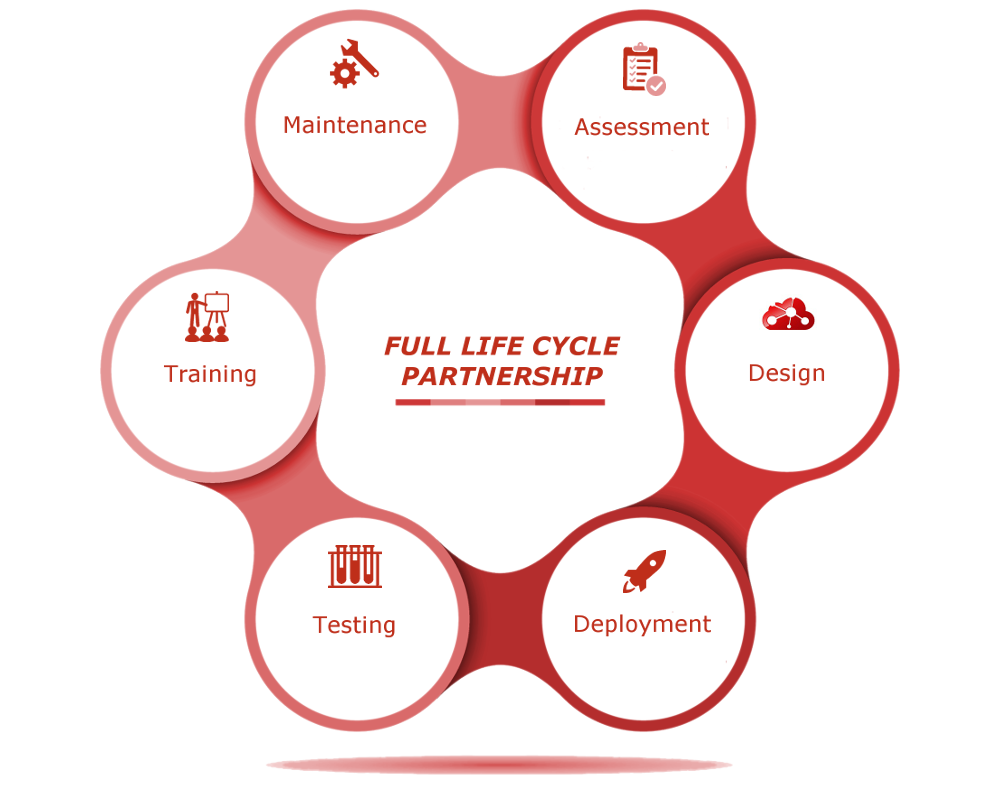
Assessment: Prioritizing your challenges and helping you choose the best way to meet them
Design: Building on your existing infrastructure to meet your evolving requirements
Deployment: Integrating, providing, and installing all new hardware and software
Testing: Ensuring the solution meets both specifications and expectations
Training: Making sure your staff can fully and effectively use new systems
Maintenance: Keeping systems up to date and performing to service level agreements (SLAs)


